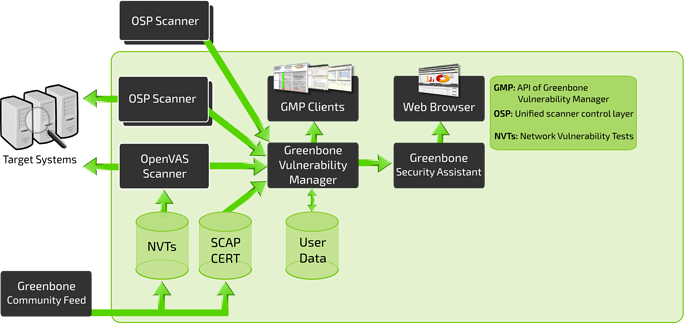
Greenbone maintains a public feed of Network Vulnerability Tests (NVTs) for OpenVAS. This public feed is called the Greenbone Community Feed (GCF). You will find it at the bottom left of the GVM-10 architecture overview:
It contains more than 50,000 NVTs, growing on a permanent basis. This feed is configured as the default for OpenVAS. It is a subset of the Greenbone Security Feed (GSF) which is part of the commercial Greenbone Security Manager appliance products.
Browse all vulnerability tests of the GSF at the public SecInfo Portal
GCF and GSF share the same base set of NVTs and both are daily updated. The common base includes immediate availability of “Hot NVTs” which address security problems running fast through the Internet and through the press.
However, the GCF receives no new NVTs for features for enterprise environments since September 4th 2017. This distinction is regarded an adequate balance between community needs and commercial needs.
For online-synchronisation use the command line tool greenbone-nvt-sync to update your local NVTs with the newest ones from the feed service. This tool in included in the OpenVAS module.
The files of the GCF are signed by the “GCF Transfer Integrity” certificate. It is intended to assist you in verifying the integrity of the NVT files after transfer. You can also activate OpenVAS to verify the integrity. A valid signature only means that the script has not been modified on the way
between the distribution point and your installation. More details and how to use it see: